OAuth 2.0 (Open Authorization 2.0) is an industry-standard protocol for authorization that provides a secure and delegated access mechanism, allowing third-party applications to access a user’s data without sharing credentials. It is widely used for enabling secure access to APIs (Application Programming Interfaces) and ensuring that user credentials are not exposed to unauthorized parties.
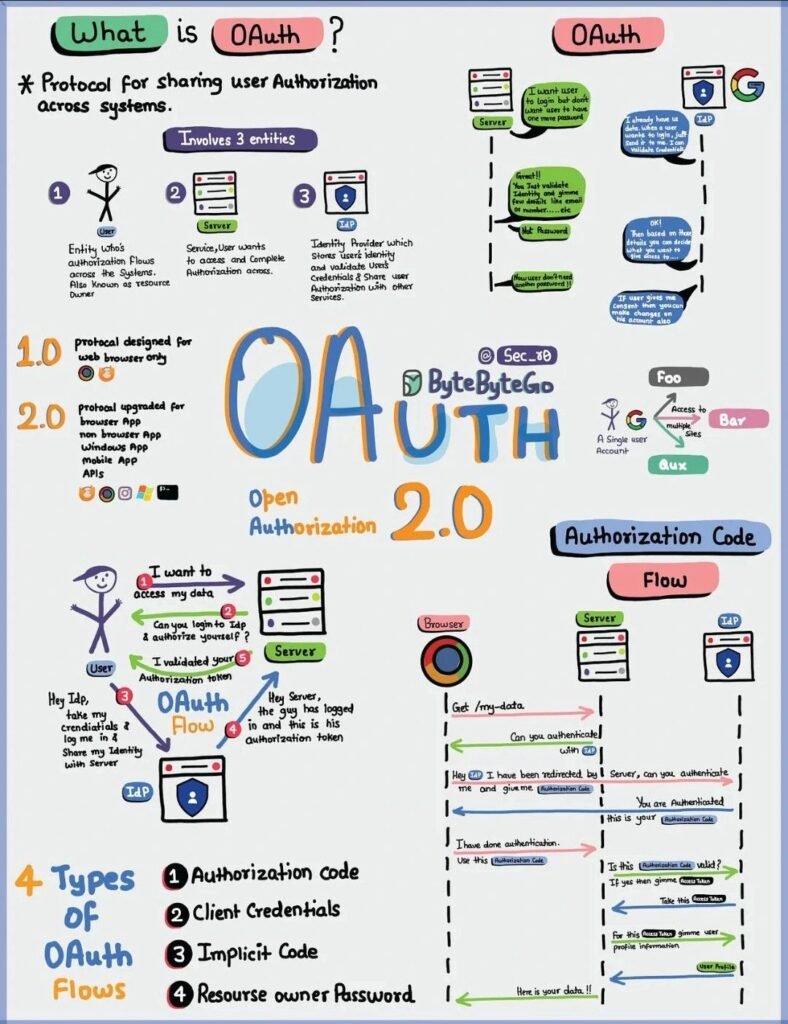
Here are key components and concepts associated with OAuth 2.0:
1. Roles:
- Resource Owner: The user who owns the data and grants access to a third-party application.
- Client: The application requesting access to the user’s data.
- Authorization Server: The server responsible for authenticating the user and granting access tokens.
- Resource Server: The server hosting the protected user data that the client wants to access.
2. Authorization Grant Types:
- OAuth 2.0 defines several authorization grant types, each suitable for different use cases:
- Authorization Code Grant: Used for web applications. After the user is authenticated, the authorization server provides an authorization code to the client, which is then exchanged for an access token.
- Implicit Grant: Suitable for mobile or single-page applications. The access token is returned directly to the client without exchanging an authorization code.
- Client Credentials Grant: Used for machine-to-machine communication. The client uses its credentials to obtain an access token directly.
- Resource Owner Password Credentials Grant: In this case, the user’s credentials (username and password) are exchanged directly for an access token. This grant type is typically used with highly trusted applications.
3. Access Tokens:
- Access tokens are the keys to accessing protected resources on behalf of the resource owner.
- They can have different scopes, indicating the level of access granted (e.g., read-only, read-write).
- Access tokens have an expiration period for security reasons.
4. Refresh Tokens:
- Refresh tokens are optional and can be used to obtain a new access token without requiring the user to re-authenticate.
- They are useful for long-term access, and their usage depends on the authorization server’s policies.
5. Endpoints:
- OAuth 2.0 defines several endpoints that clients and servers use to interact:
- Authorization Endpoint: Where the resource owner grants authorization to the client.
- Token Endpoint: Used by the client to exchange an authorization grant for an access token.
- Redirection Endpoint: Where the authorization server sends the user after a successful authorization.
6. Scopes:
- Scopes define the permissions associated with an access token. Clients request specific scopes during the authorization process.
7. Security Considerations:
- OAuth 2.0 provides mechanisms for securing communications, but implementers must be aware of potential vulnerabilities, such as token leakage or insufficient protection during transmission.
OAuth 2.0 is widely adopted due to its flexibility, security, and support for various use cases. It is employed by major internet companies and platforms to facilitate secure and controlled access to user data by third-party applications. As with any security protocol, it’s crucial for developers to implement OAuth 2.0 correctly to ensure the protection of user data and credentials.


















4 Responses
Your point of view caught my eye and was very interesting. Thanks. I have a question for you.
Thanks!, Please let me know if you have any question related to this topic or any topic in cybersecurity.
perferendis et neque temporibus rerum error possimus. hic atque sunt cupiditate amet qui earum voluptatem laboriosam.
Great article! I appreciate the clear and insightful perspective you’ve shared. It’s fascinating to see how this topic is developing. For those interested in diving deeper, I found an excellent resource that expands on these ideas: check it out here. Looking forward to hearing others’ thoughts and continuing the discussion!